Why Ransomware Hits Manufacturers Harder Than Anyone Talks About
Ransomware coverage tends to focus on healthcare and financial services. Those sectors make headlines because patient data and financial records are visible, regulated, and easy to explain to a general audience. But manufacturing is consistently one of the most targeted industries in ransomware campaigns, and the damage is often worse because the conversation about OT security in the mid-market has barely started.
If you run or manage security for a manufacturing operation, this is worth understanding before an incident forces the conversation.
The OT Environment Is Different
Most cybersecurity tools, practices, and frameworks were built for IT environments. Servers, workstations, Active Directory, cloud infrastructure — the traditional enterprise attack surface. Operational technology is a different category entirely.
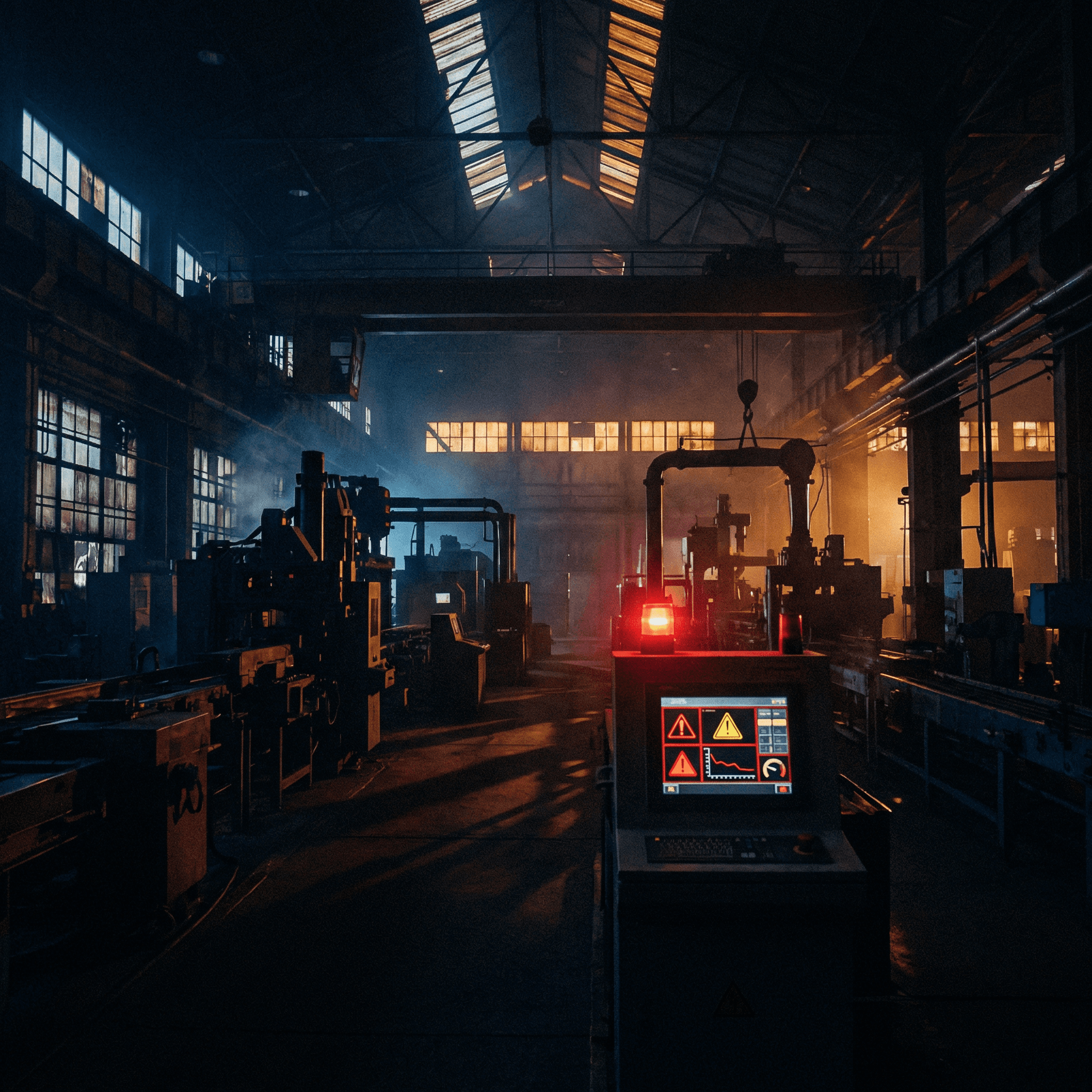
OT encompasses the systems that control physical processes. Programmable logic controllers that run production lines. SCADA systems that monitor and manage industrial equipment. HMI terminals that operators use to interact with machinery. Sensors and actuators that feed data into manufacturing execution systems.
These systems were designed for reliability and uptime, not security. Many of them run operating systems that are no longer supported. Many cannot be patched without taking the production line offline, which means patch windows are infrequent or nonexistent. Many were installed a decade or more ago with the assumption that physical isolation from the corporate network was sufficient protection. That assumption has not held up as IT and OT networks have converged.
What Happens When Ransomware Hits an OT Environment
When ransomware spreads from an IT environment into OT systems, the impact is not a locked file server. It is a stopped production line. Equipment that cannot be operated. Orders that cannot be filled. Contracts that are in jeopardy. In some cases, physical equipment that has to be inspected or recalibrated before it can be safely restarted.
The financial calculation is different from a typical IT ransomware event. A manufacturer running three shifts at full capacity losing two weeks of production is not calculating ransom payment against data recovery cost. They are calculating ransom payment against production loss, contract penalties, customer relationships, and potential equipment damage. The math changes the decision.
This is why ransomware groups specifically target manufacturers. The pressure to pay is higher because the cost of downtime is higher.
Why Most MSSPs Cannot Help With This
Traditional managed security services were built around IT environments. EDR on endpoints, SIEM ingesting network and server logs, firewall monitoring, email security. That coverage model does not translate directly to OT.
You cannot install a standard EDR agent on a PLC. You cannot apply patches to a SCADA system on a normal schedule. You cannot run aggressive vulnerability scanning against OT systems without risking disrupting the processes they control. The tools and techniques that work in IT environments can cause the exact problems in OT environments that you are trying to prevent.
Effective OT security requires passive monitoring approaches that observe network traffic and system behavior without querying or interacting with sensitive control systems directly. It requires platforms purpose-built for OT visibility — Nozomi Networks, Claroty, and Dragos are the recognized leaders in this space. And it requires practitioners who understand the difference between an IT security incident and an OT security incident, because the response is not the same.
What Good OT Security Looks Like for Mid-Market Manufacturers
The starting point for most mid-market manufacturers is network segmentation. IT and OT networks should be separated, with controlled and monitored pathways between them. This is not always in place, and in many manufacturing environments the IT and OT networks have converged organically over years of operational decisions that prioritized convenience over security.
Once segmentation is in place or being planned, passive OT monitoring provides visibility into what is happening on the production network without putting operational systems at risk. These platforms identify devices, map communication patterns, and alert on anomalous behavior — the same function a SIEM performs on an IT network, built for OT constraints.
Vulnerability management in an OT environment requires a different approach. Scanning has to be done carefully, with awareness of which systems are sensitive to query traffic and which can tolerate it. The output is a risk-prioritized list that accounts for the operational reality of patching, not just the technical severity of the finding.
And incident response planning for a manufacturer has to account for OT-specific scenarios. A tabletop exercise that only covers IT systems leaves the most consequential part of the environment unaddressed.
The Conversation That Needs to Happen
If you manage security for a manufacturing operation and your current MSSP has never asked about your OT environment, that is a gap. Not because they are doing a bad job on the IT side, but because the IT side is not the whole picture.
The convergence of IT and OT is real, it is accelerating, and it is creating attack paths that did not exist five years ago. Ransomware groups have noticed. The mid-market manufacturers who get ahead of this are the ones who have the conversation before an incident forces it.