MSP vs MSSP: Why the Difference Matters More Than You Think
Most small and mid-size businesses have a managed service provider. They handle the helpdesk tickets, manage the servers, keep the printers talking to the network, and make sure email stays running. For a lot of organizations, that relationship feels like security coverage. It is not.
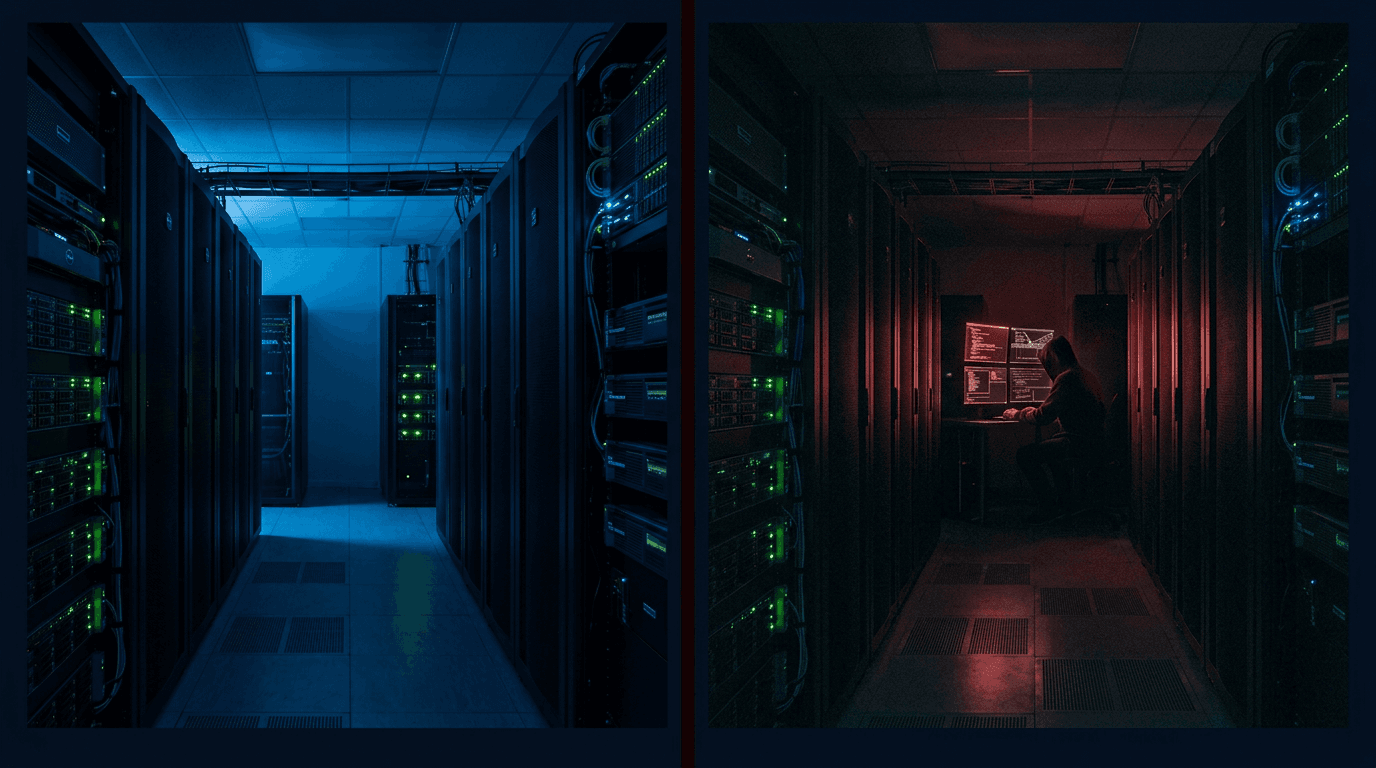
The confusion is understandable. MSPs and MSSPs both manage technology on your behalf, both show up in your vendor list, and both use the word "managed" in their name. But the scope of what they are responsible for is fundamentally different, and that difference is exactly where attackers look for their opening.
What an MSP Is Responsible For
A managed service provider is focused on availability and performance. Their job is to make sure your systems are up, your users can work, and your infrastructure is functioning the way it is supposed to. They monitor uptime, manage patches on a schedule, handle hardware replacements, and respond when something breaks.
When it comes to your firewall, an MSP will make sure it is turned on, passing traffic, and has a basic policy in place. That is a reasonable scope for an infrastructure management contract. It is not a security posture.
What an MSSP Is Responsible For
A managed security services provider is focused on threat. Their job is to understand what your environment looks like to an attacker, monitor for activity that indicates something is wrong, and respond before damage is done.
When it comes to your firewall, an MSSP looks at the policy itself. Not just whether it is running, but whether the rules make sense. Whether there are entries that were added for a development project two years ago and never cleaned up. Whether someone opened a port to "make something work for now" and that exception became permanent. Whether the log output is showing traffic patterns that suggest reconnaissance or lateral movement.
Those two approaches — is it running versus is it secure — produce very different outcomes when something goes wrong.
The Gap Is Where Breaches Happen
Most successful attacks do not exploit exotic zero-day vulnerabilities. They exploit the space between what an organization thinks is covered and what is actually being watched. An unmonitored endpoint. A firewall rule that should have been removed. A login attempt that triggered no alert because nobody was looking at the logs.
This is not a criticism of MSPs. Availability management is a legitimate and valuable service. The problem is when organizations assume that having an MSP means having security coverage. Those are different contracts, different skill sets, and different responsibilities.
If your MSP has never reviewed your firewall policy for unnecessary rules, never run a vulnerability scan against your external perimeter, never delivered a report showing you which of your endpoints are missing EDR coverage, and never escalated an alert at 2am because something looked wrong — you have infrastructure management. You do not have security management.
Why This Matters for SMBs Specifically
Large enterprises figured this out a long time ago. They have separate teams, separate vendors, and separate budgets for infrastructure operations and security operations. Mid-market and small businesses often cannot afford that separation, so the lines blur.
The result is that a 150-person manufacturing company in Tampa is running the same firewall policy that was set up in 2019, with no visibility into whether it is actually blocking what it is supposed to block, and no monitoring of the log output that would show them if someone was trying to get in. Their MSP is keeping the lights on. Nobody is watching the door.
This is the gap that 9 Realms Security was built to close. Enterprise-grade security operations, delivered at a price point that works for organizations that have been underserved by both the large integrators and the local resellers. Human analysts watching your environment around the clock. Firewall policies that get reviewed, not just maintained. Alerts that go to someone who acts on them, not a queue that nobody checks.
What to Do If You Are Not Sure
Ask your current provider a simple question: when was the last time someone reviewed my firewall policy for unnecessary rules? If the answer is uncertain, or if the question gets redirected to a conversation about your service contract, you have your answer.
Security is not a byproduct of good infrastructure management. It requires a different kind of attention, different tools, and a different mandate. Make sure the vendor you are paying for security is actually responsible for it.